Google Cloud Storage (GCS)¶
Pre-requisites¶
To create an Instance Secret for securing GCS credentials, you must have the following information:
Access Permissions in DataOS¶
To create an Instance Secret in DataOS, at least one of the following role tags must be assigned:
-
roles:id:data-dev -
roles:id:system-dev -
roles:id:user
Checking Assigned Roles
Use the following command to verify assigned roles:
If any required roles are missing, contact a DataOS Operator or submit a Grant Request for role assignment.
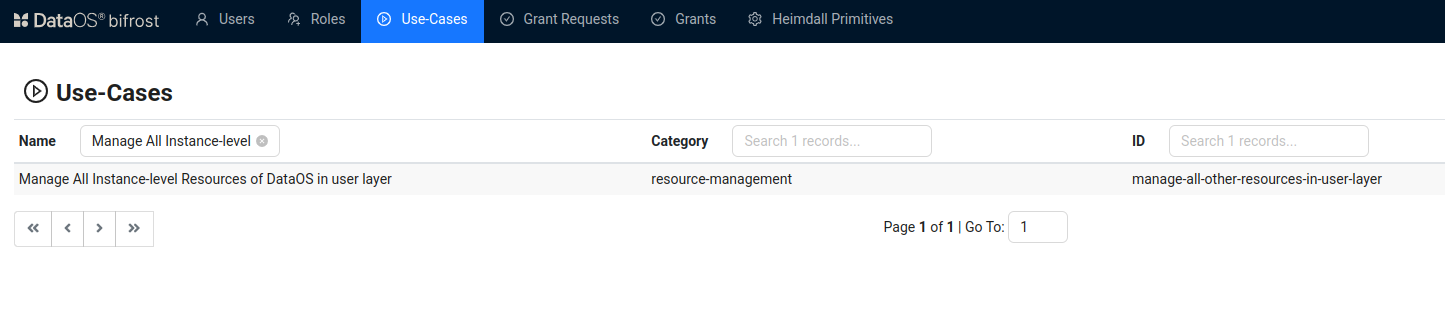
Alternatively, if access is managed through use cases, ensure the following use case is assigned:
-
Manage All Instance-level Resources of DataOS in User Layer
To validate assigned use cases, refer to the Bifrost Application Use Cases section.
Bifrost Governance
Source System Requirements¶
-
Project ID for the Google Cloud Project: The unique identifier of the Google Cloud project where your GCS bucket resides. You can retrieve this from the Google Cloud Console by navigating to your project dashboard and locating the *Project ID- under project information.
-
Email Address Associated with the Google Cloud Service Account: The email address of the service account used to authenticate and access your GCS bucket. This can be found in the IAM & Admin > Service Accounts- section of the Google Cloud Console by selecting the service account and viewing its details.
-
JSON Key File for the Google Cloud Service Account: The path to the JSON key file used to authenticate the service account. To obtain this, navigate to IAM & Admin > Service Accounts- in the Google Cloud Console, select the relevant service account, click Keys, and download the JSON key file by selecting Add Key > JSON. Ensure the file is stored securely, and note its path.
Ensure you have these credentials ready before proceeding with the Instance Secret creation process.
Create an Instance Secret for securing GCS credentials¶
Google Cloud Storage (GCS) is an object storage system. Object stores are distributed storage systems designed to store and manage large amounts of unstructured data.
To create a Google Cloud Storage (GCS) Instance Secret in DataOS, ensure you have access to the DataOS Command Line Interface (CLI) and the required permissions. Follow the steps below to complete the creation process efficiently and securely.
Step 1: Create a manifest file¶
Begin by creating a manifest file to hold the configuration details for your GCS Instance Secret. Depending on your access needs (read-only or read-write), start with the corresponding YAML template provided below.
name: ${gcs-depot-name}-r # Name of the instance-secret, indicating it's for read-only access.
version: v1 # Version of the instance-secret.
type: instance-secret # Specifies that this is an instance-secret.
description: ${description} # Optional: Brief description of the instance-secret's purpose.
layer: user # DataOS layer where the secret is assigned.
instance-secret:
type: key-value-properties # Type of Instance-secret, stored as key-value pairs.
acl: r # Access control level, set to 'r' for read-only access.
data:
projectid: ${project-id} # Unique identifier of the Google Cloud project that your GCS bucket resides in.
email: ${client-email} # Email address associated with the Google Cloud service account.
files:
gcskey_json: ${path-to-gcskey-json} # Path to the JSON key file for the Google Cloud service account.
name: ${gcs-depot-name}-rw # Name of the instance-secret, indicating it's for read-write access.
version: v1 # Version of the instance-secret.
type: instance-secret # Specifies that this is an instance-secret.
description: ${description} # Optional: Brief description of the instance-secret's purpose.
layer: user # DataOS layer where the secret is assigned.
instance-secret:
type: key-value-properties # Type of Instance-secret, stored as key-value pairs.
acl: rw # Access control level, set to 'rw' for read-write access.
data:
projectid: ${project-id} # Unique identifier of the Google Cloud project that your GCS bucket resides in.
email: ${client-email} # Email address associated with the Google Cloud service account.
files:
gcskey_json: ${path-to-gcskey-json} # Path to the JSON key file for the Google Cloud service account.
Resource meta section
The GCS manifest includes a Resource meta section with essential metadata attributes common to all resource types. Some attributes in this section are optional, while others are mandatory. For more details, refer to the configurations section.
Instance-secret specific section
This section focuses on attributes specific to GCS Instance Secrets. It includes details like:
-
type: Specifies the Instance Secret type (key-value-properties). -
acl: Access control level (read-only or read-write). -
data: Contains sensitive information such as Azure endpoint suffix, storage account key, and storage account name.
For more information, refer to the configurations section.
Step 2: Apply the manifest¶
Warning
If the connection credentials contain special characters such as @ : / ? # & = + ; % \ ' { } ( ) * $ !, the --disable-interpolation flag must be used when applying instance-secrets or secrets. This ensures that special characters are retained as-is in the string.
Example:
To create the GCS Instance Secret within DataOS, use the apply command. Since GCS Instance Secrets are Instance-level resources, do not specify a workspace while applying the manifest.
Step 3: Validate the Instance Secret¶
To validate the proper creation of the Instance Secret in DataOS, use the get command.
To get the list of all the Instance Secret within the DataOS environment execute the following command.
dataos-ctl resource get -t instance-secret -a
INFO[0000] 🔍 get...
INFO[0000] 🔍 get...complete
NAME | VERSION | TYPE | WORKSPACE | STATUS | RUNTIME | OWNER
-----------------------------|---------|-----------------|-----------|--------|---------|------------------------
abfssv2alpha-r | v1 | instance-secret | | active | | iamgroot
abfssv2alpha-rw | v1 | instance-secret | | active | | iamgroot
abfsswithoutmetastore-r | v1 | instance-secret | | active | | thisisthor
abfsswithoutmetastore-rw | v1 | instance-secret | | active | | thisisthor
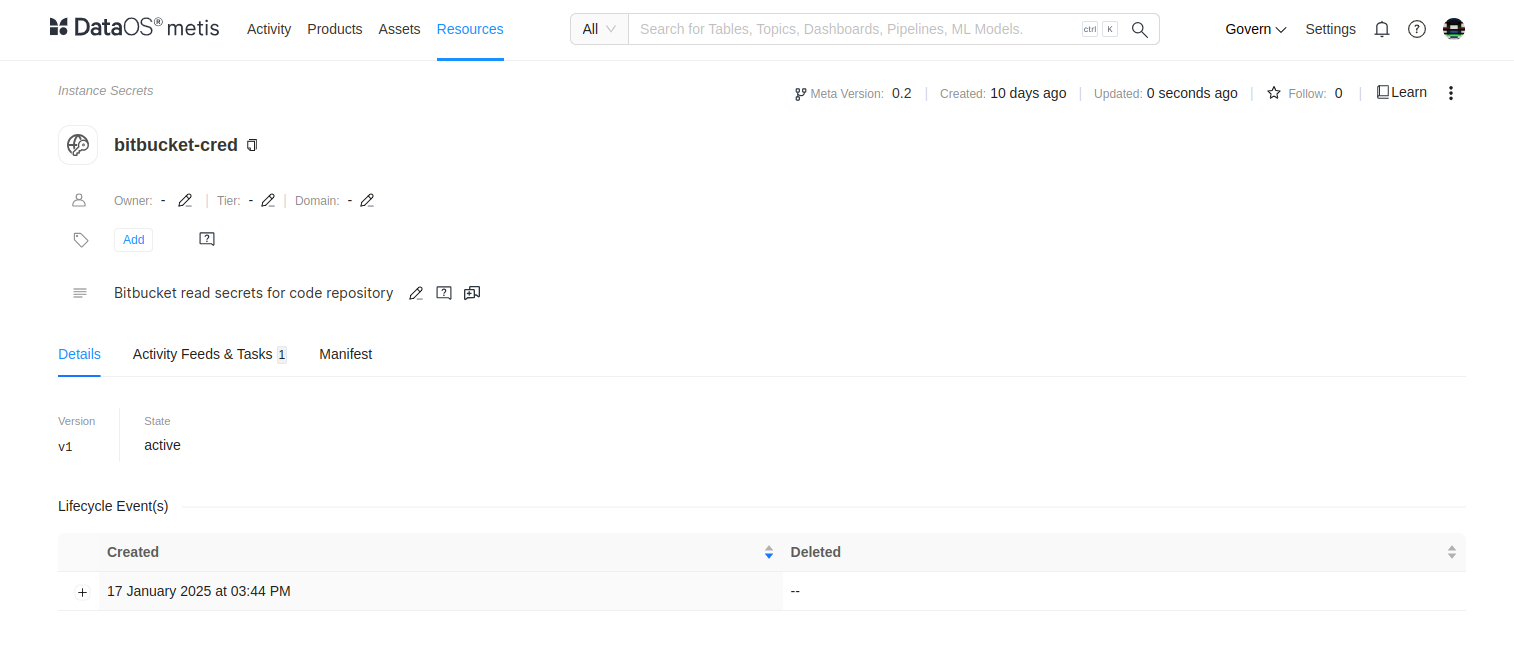
Alternatively, you can also check on Metis UI by searching the Instance Secret by name.
Delete the Instance Secret¶
To delete an Instance Secret, use one of the following methods:
Method 1¶
Specify the Resource type and Instance Secret name in the delete command.
Method 2¶
Copy the Instance Secret name, version, and Resource-type from the output of the get command separated by '|' enclosed within quotes and use it as a string in the delete command.
Method 3¶
Specify the path of the manifest file and use the delete command.